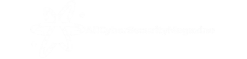
In June 2025, cryptographers from MIT reported strange decryption anomalies across encrypted financial records, potentially signaling early-stage quantum-assisted brute force attempts.
While fully capable quantum computers are still years out, hybrid attacks using quantum- inspired algorithms on classical systems are emerging. These target weak keys and flawed entropy in legacy systems.
Financial institutions and government bodies are advised to begin migration toward post-quantum cryptographic standards. NIST’s PQC algorithm suite is the new baseline.
Delaying quantum defense is no longer theoretical risk — it may already be exploited.
Recent News
© 2025 AllCyberSecurityMagazine - Nigeria's premier source for cybersecurity news.